Research shows that US travelers pay more for their holiday
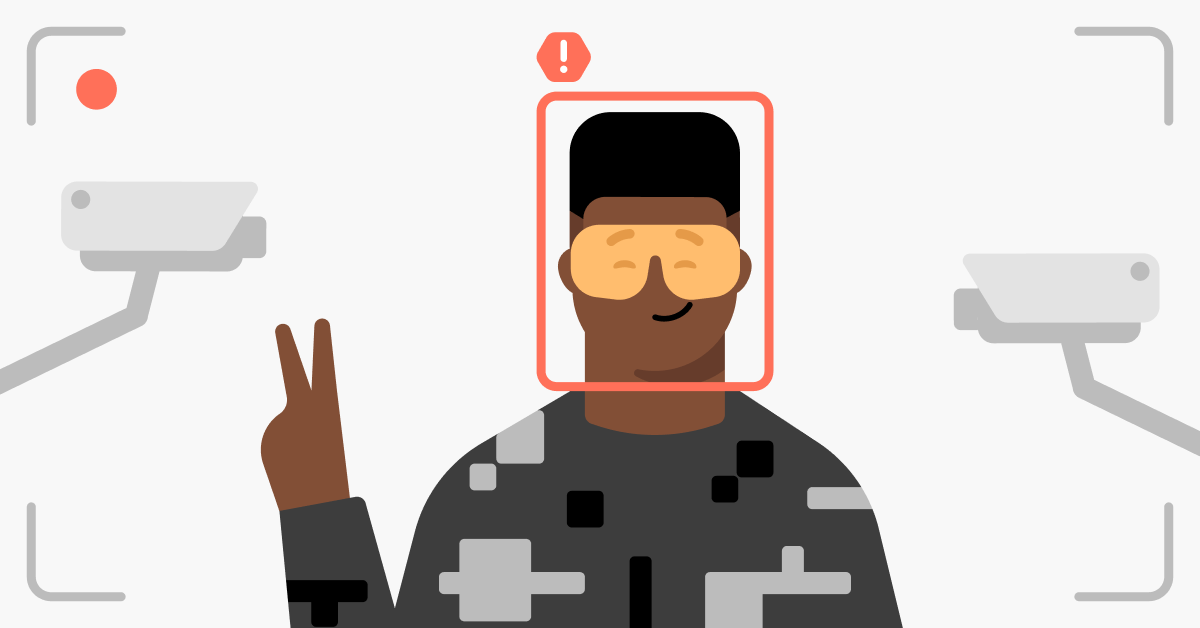
Research from NordVPN has uncovered that US travelers often pay hundreds of dollars more than international customers when booking vacations through local websites. This price discrepancy affects popular holiday services, including car rentals and hotel stays. We'll explore these findings and show you how using a VPN can help secure a more affordable holiday.
Apr 30, 2024
6 min read
Violeta Lyskoit
Popular articles
Apr 27, 2024
1 min read
Is it safe to use hotel Wi-Fi? Hotel network security explained
Recent articles
Apr 30, 2024
6 min read
Australians can expect to pay up to 128% more for travel arrangements
Apr 30, 2024
6 min read
Research shows that Canadian travelers pay up to 46% more for holiday services