What is a deauthentication attack, and how does it work?
A deauth or deauthentication attack disrupts connections between users and Wi-Fi access points. The attackers force devices to lose access and then reconnect to a network they control. Then, perpetrators can capture login details or trick users into installing rogue programs. Learn more about how deauthentication attacks work and how you can mitigate their impact.

Table of Contents
Table of Contents
What is a deauthentication attack?
A deauthentication attack is a type of denial of service attack interfering with communication between routers and devices. It exploits IEEE 802.11 wireless networks as they have the necessary deauthentication frames. Networks use them to end connections or, in other words, disconnect users.
The issue begins when networks cannot verify the source of deauth frames. Deauthentication attacks imitate these frames and force targeted users to go offline. Since such Wi-Fi access points do not properly authenticate termination requests, it closes connections.
Due to security gaps in management frames, deauth attacks are possible even with modern network security keys (like WPA2). For instance, perpetrators can capture WPA/WPA2 4-way handshake and use commands like aireplay-ng -0 to deauthenticate wireless users.
How do deauth attacks work?
Essentially, a deauthentication attack works through the following steps:
- Some Wi-Fi networks do not have effective mechanisms for verifying MAC addresses.
- Perpetrators spoof MAC addresses and send deauthentication frames, forcing the client offline.
- If attackers continue sending forged frames after they terminate connections, users won’t be able to reconnect. While the attack could focus on a single target, it might also jam the wireless networks. Thus, all connected clients go offline.
- Attackers can set up rogue networks or evil twins mimicking legitimate access points so they can watch victims’ traffic. This surveillance covers all communications, visited websites, and financial transactions.
When can a deauthentication attack occur?
Let’s take a look at a few situations where deauth attacks could occur.
Forcing hidden cameras to go offline
Over the years, frequent disputes forced Airbnb to forbid the use of cameras in rented apartments or rooms. Yet, more cunning homeowners can conceal cameras from their guests.
White hackers emphasize that deauthentication attacks can reveal whether a rented apartment conceals cameras.
Hotels that push paid Wi-Fi
There have been incidents when hotels employed deauthentication attacks to promote their Wi-Fi services. In fact, the Federal Communications Commission (FCC) issued documents stating that blocking or interfering with Wi-Fi hotspots is illegal.
One of the first offenders was the Marriott hotel. It had financial motives for disrupting visitors’ access points. However, charging perpetrators with deauthentication attacks is a rare sight. Usually, victims might blame the interruptions on unstable Wi-Fi.
Susceptible smart devices
Criminals could push connected devices offline for several reasons. One danger is that attackers might disable security systems.
Thus, such interruption halts monitoring of the home, office, or other areas. In worst-case scenarios, such deauth attacks could help burglars.
Another example comes from a vulnerability in Ring Video Doorbell Pro (now fixed). The exploited flaw means using a Wi-Fi deauthentication attack to force the device to re-enter the configuration mode. Then, eavesdroppers can capture Wi-Fi credentials orchestrated to travel in an unencrypted HTTP.
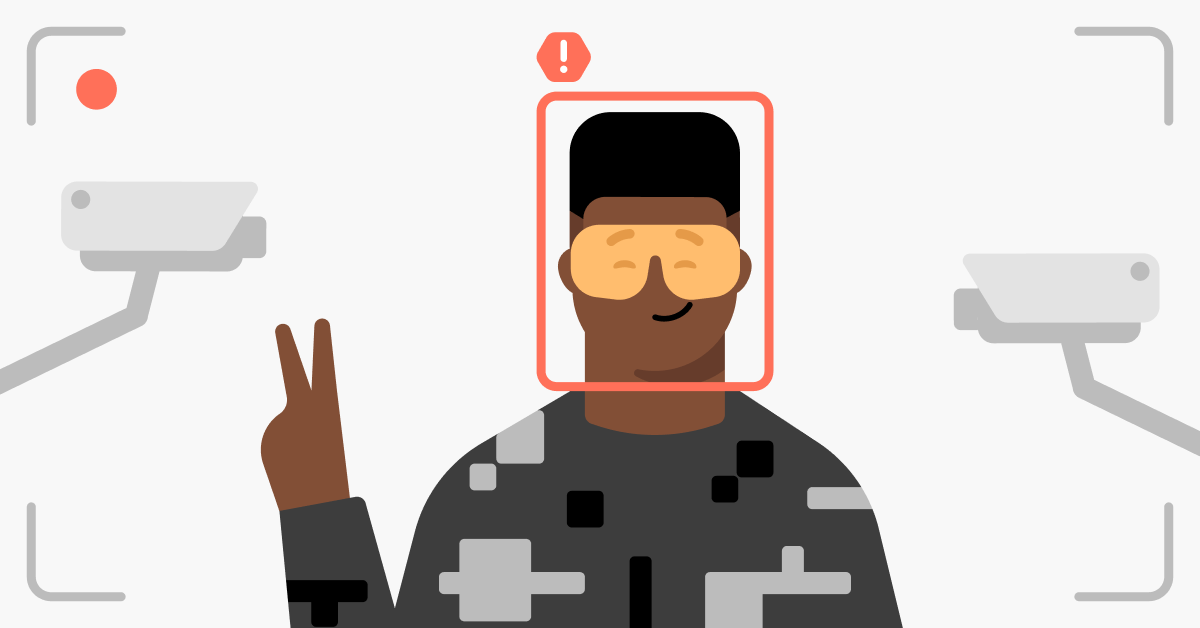
Forcing users to join evil twins
Spoofed deauthentication frames force targeted devices to drop their connection. It could be a way to break the legitimate connection and trick users into joining fake hotspots.
Deauth attacks could flood the access point so that devices cannot join for a period of time.
How to prevent deauthentication attacks
The prevention of deauthentication attacks does not offer many options. But there are effective strategies for mitigating their impact.
- Ensure that your network applies WPA2 encryption. If you use a pre-shared key, it must be complex and lengthy to withstand threats like brute-force attacks.
- Another improvement might be 802.11w. It validates deauthentication frames and discards spoofed ones. Older hardware and IoT might not support it, raising issues for some Wi-Fi clients.
- Furthermore, remember you have minimal control over free public Wi-Fi and its security, so it could be beneficial to use a VPN.
A VPN can assist if deauthentication attacks force clients to connect to evil twins. NordVPN creates a secure path between users and access points. Encrypted traffic will prevent attackers from capturing any meaningful communications or data.
Remember, legitimate public Wi-Fi hotspots can lack encryption, too. Therefore, enable a VPN every time you join an unknown network.